Resources
Resource Library
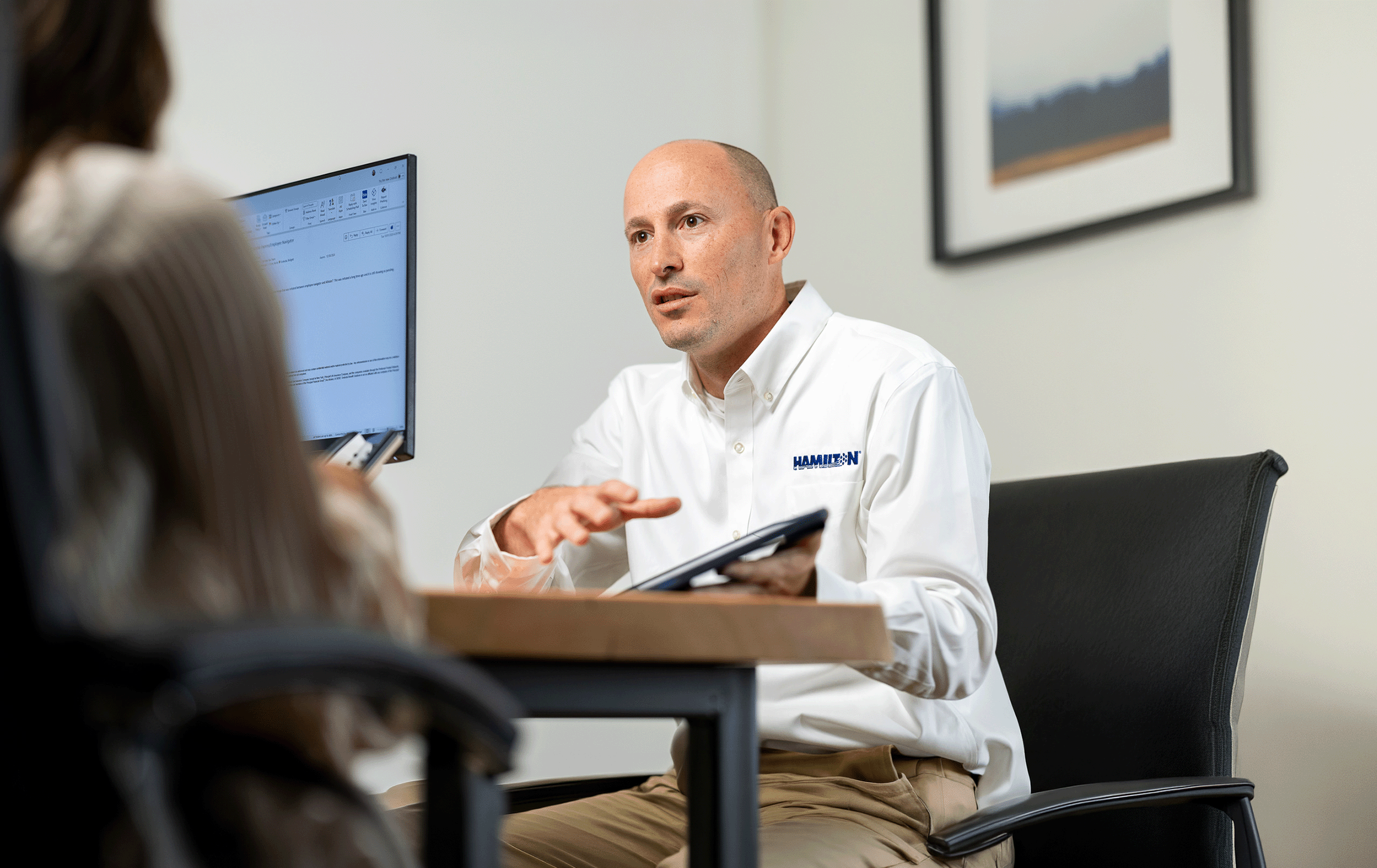
Whether you are looking for the latest information on business technology trends or seeking guidance and insights from our industry experts, our resources are a great place to browse. Read our latest blogs, listen to interviews with our experts or browse our informational flyers and white papers. Can’t find what you are looking for? Send us an email at info@hamiltonisbusiness.com for a one-on-one free consultation.
OUR LATEST INSIGHTS
Updating your communications isn’t just about new tech—it’s about creating better conversations with customers and simplifying work for your team. Whether you’re moving away from legacy desk phones or fine-tuning a cloud setup, modernizing your business telecommunications systems can improve reliability, [...]
Artificial intelligence (AI) has moved from a buzzword to something that is used by many in everyday conversations. AI has become a practical set of tools that can streamline operations, elevate customer experience and open new sources of revenue. If you’re [...]
OUR RESOURCES
Cyber threats continue to accelerate in speed, volume and sophistication. In response, Artificial Intelligence (AI) and cybersecurity are converging to deliver faster detection, smarter analysis and more resilient defense. Organizations must learn to harness machine learning and automation to uncover anomalies, [...]
In the fast-paced digital age, every business relies on technology to succeed. As systems become more intricate, understanding the difference between observability and monitoring is crucial. While both observability tools and monitoring tools aim to enhance system performance and reliability, they [...]
Recently, Hamilton CEO, John Nelson sat down with the hosts of “Business Builders” at 93.7 The Ticket Talk Radio in Lincoln, Nebraska to discuss strategies for transforming small ideas into sustainable business. With 125 years of experience in the telecommunications industry, [...]
Phishing emails are a major threat to businesses and hackers are getting more creative as each day passes. Recognizing these common techniques is essential for protecting yourself and your organization from security breaches. Here are some tips to help recognize these [...]
In today's fast-paced digital world, keeping up with technology is more than just upgrading hardware or ensuring software is up to date. It’s about equipping your employees with the knowledge they need to stay secure in an ever-evolving digital landscape. Read [...]
As a business owner, you know the difficulty involved in trying to keep up with industry regulations, managing your risks and ensuring operational efficiency. Governance, Risk and Compliance (GRC) is a structured approach that integrates your goals with these elements to [...]